Network Monitoring with a LAN Tap
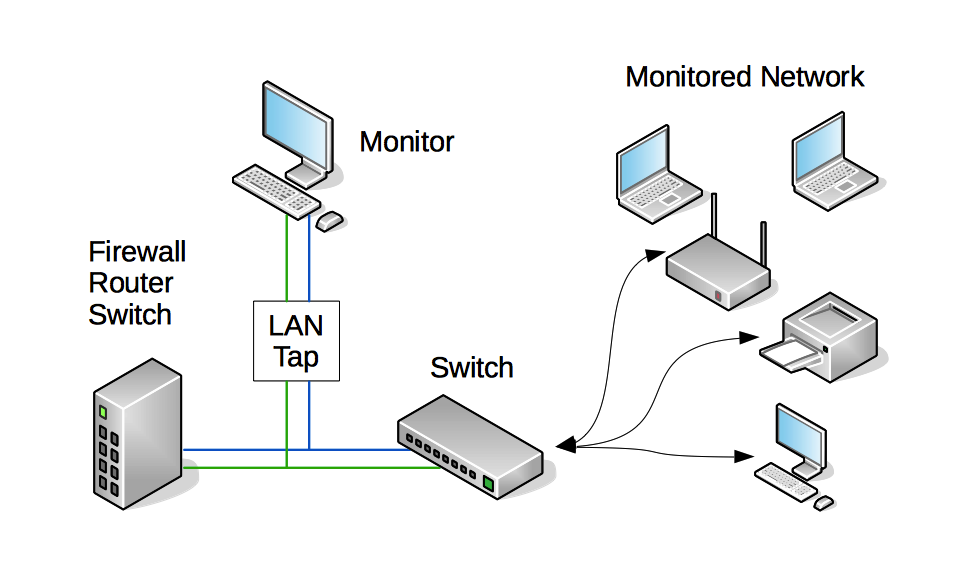
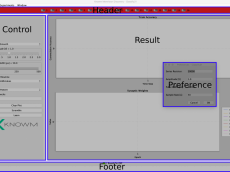
Shown in the following figure is how a LAN tap and monitoring system can be integrated into an existing network. A LAN tap is inserted between the firewall/router/switch and an internal networking switch or router. The monitor device will be able to “see” all the traffic coming into the network and going out of the network and allow for packet analysis with various tools such as WireShark, Snort or Bro. The “monitored network” could be a single computer or an entire array of hosts including those connected wirelessly. The passive tap can be placed anywhere in the system and multiple taps and monitoring devices can be deployed as well. The tap can even sit in front of the firewall.
Passive LAN Tap
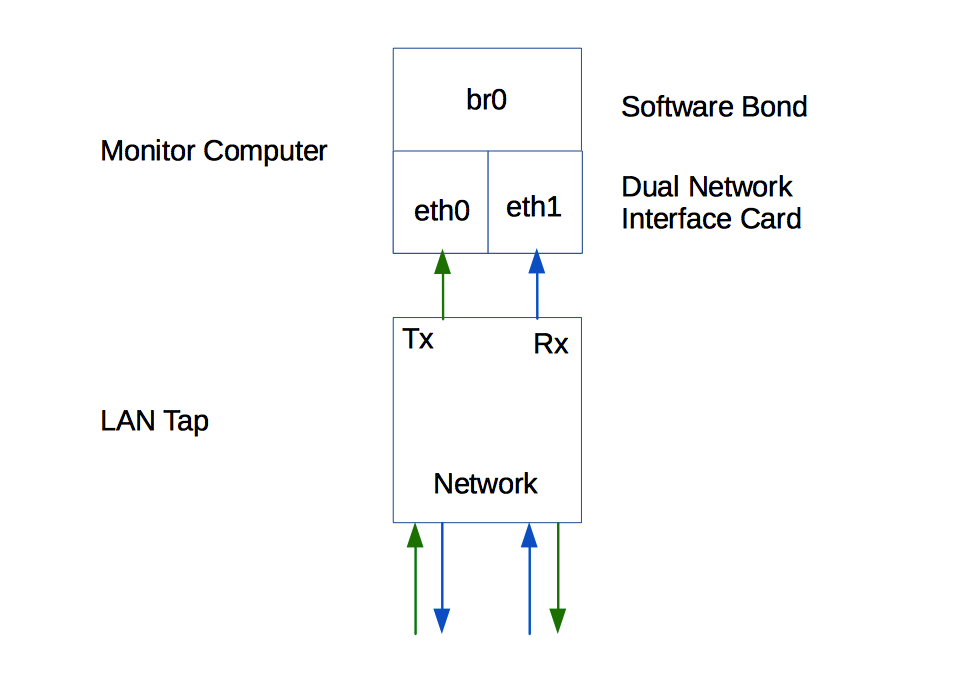
Passive LAN taps essentially allow all traffic on a network device to be monitored. Passive LAN taps are also very useful for passive network troubleshooting and analysis. Further, the tap makes a related intrusion detection system more secure, preventing attackers from being able to directly attack the IDS system since there is no outside facing network port. A passive LAN tap will create two channels though, one for each traffic flow direction. This requires two network interface cards and software to bond the channels back together into one.
Some examples:
SharkTap Network Sniffer
SharkTap Gigabit Network Sniffer
Throwing Star LAN Tap
Alternative LAN Taps
An aggregator LAN tap is tap device that bonds the channels together via hardware requiring only one network card port on the monitor computer. Aggregator taps are very expensive, however they are convenient and efficient because no port bonding is necessary on the monitor computer.
For 1000 Mbps (Gigabit) networks, an active LAN tap is necessary, as the passive network LAN tap can only handle up to 100 Mbps traffic. These expensive alternatives are best for high-speed networks with heavy traffic and can run upward to $1000 or more.
Mirror ports or span ports are found on most enterprise switches and internally copy the activity on one or more ports and make it available on a single aggregated port containing both the RX and TX traffic. Like aggregator taps, no port bonding is necessary. Span ports are low cost because they are integrated into switches, however they put strain on the network switch’s hardware and are known to suffer from a bit of packet loss.
Dualcomm 10/100/1000Base-T Gigabit Ethernet Network TAP
Dualcomm ETAP-2205 Dual-Link 10/100/1000Base-T Ethernet Network Tap
Dualcomm ETAP-2206 Dual-Link GbE Copper & Fiber Ethernet Network Tap
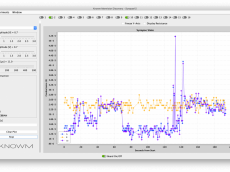
Bonding Channels for Passive Taps
When using a passive or active LAN tap and not an “aggregator” or “mirror port”, both the ‘incoming’ and ‘outgoing’ channels need to be bonded together for IDS systems to process as a single network flow channel. This setup involves using a technique called bonding to take two physical interfaces and bond them together, creating a logical interface that we can use for Snort as an example. For step-by-step instructions on how to set up port bonding, see How To Create a Bonded Network Interface.
Useful Links and Resources
- Implementing Networks Taps with Network Intrusion Detection Systems
- USB-Ethernet device for Linux
- Wireshark Capture using a network tap
- Ethernet channel Bonding
- Bonding in Linux
- Bonding in Linux 2
- Network Tap at Wikipedia – to physically tap into a network traffic stream. Once a tap is in place, a monitoring device can be connected to it as-needed without impacting the monitored network. The word passive in this instance means that there is no way to detect the device’s presence.
- Home setup with Snort and a network tap
- Port Mirroring is used on a network switch to send a copy of network packets seen on one switch port (or an entire VLAN) to a network monitoring connection on another switch port. Cisco calls port monitoring SPAN, which stands for Switched Port Analyzer.
- Home Passive Tap setup









Leave a Comment